Why Chrome Extensions Are a Risky Bet for Health Tech
On Christmas Day 2024, while most security teams were running skeleton crews, attackers pushed a malicious update to a Chrome extension built by Cyberhaven, a security company. The update passed Google's review process and was automatically installed on users' browsers with no action required. Within hours, the compromised extension was silently exfiltrating session cookies and authentication tokens, specifically targeting high-value accounts like Facebook Ads.
It wasn't an isolated incident. Security researchers found that more than 30 Chrome extensions were compromised in the same campaign, affecting 2.6 million users. One organization alone had 859 megabytes of data exfiltrated before anyone noticed.
This is a good reminder of why building healthcare technology on Chrome extensions is a risk most founders underestimate.
The Appeal Is Obvious
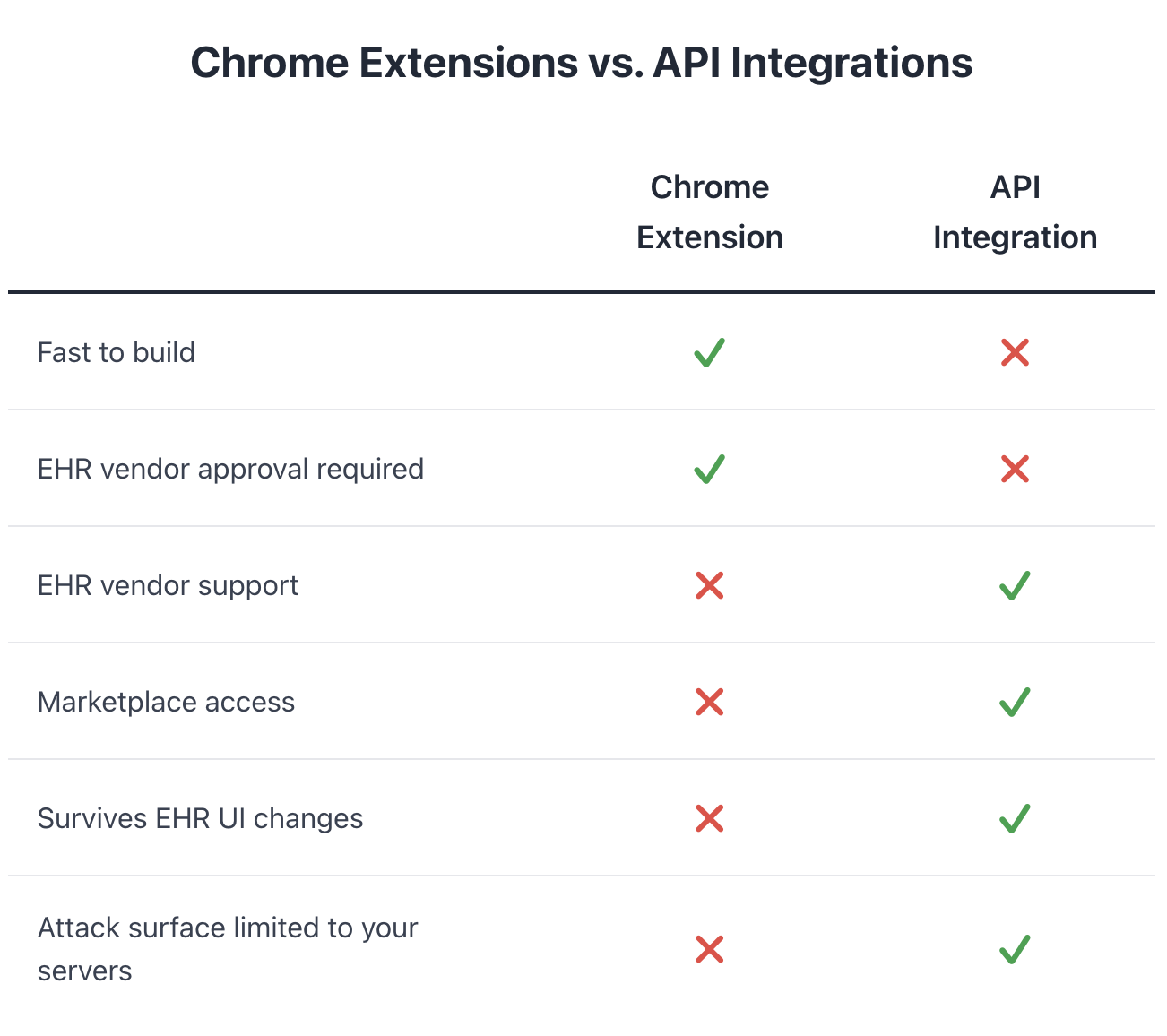
I get why health tech startups reach for Chrome extensions. They're fast to build. They can scrape data from EHR screens without waiting for API approval. They can write data back into the EMR, auto-populating notes or inserting orders. They let you move quickly when you're trying to prove out a product idea.
Whole companies have been built on this approach. Vim, for example, has created infrastructure specifically to help health tech companies build browser-based solutions that sit on top of EHRs. I'm genuinely aligned with their mission of making it easier to build and deploy health tech. That's a goal worth pursuing. But the underlying architecture carries security and platform risks that don't disappear just because the tooling is good.
For a scrappy team trying to get to market, browser extensions feel like the smart shortcut.
Why athenahealth Discourages Chrome Extensions
athenahealth strongly discourages Chrome extensions that interact with their platform. Their Service Agreement prohibits scraping and manipulating data, which most extensions rely on. This isn't arbitrary bureaucracy. It comes from years of painful experience.
When a Chrome extension breaks something in a practice's workflow, the practice doesn't call the extension vendor. They call athena. And athena's support team is stuck trying to troubleshoot a problem they can't see, caused by software they didn't build, running in an environment they don't control.
It gets worse when practices run multiple extensions. They interact in unpredictable ways, break each other, and create issues that are nearly impossible to diagnose. The blame still flows to athena.
There's also the technical reality: poorly written extensions can introduce memory leaks that slow or crash athenaOne. And every extension expands the attack surface for accessing PHI, credentials, and other sensitive data.
The Security Problem
Chrome extensions require broad permissions: reading page content, capturing keystrokes, accessing cookies, monitoring network requests. Many healthcare extensions also have write access. And even if your code is clean, a compromised dependency or hijacked developer account can push malicious code to all your users automatically. That's what happened with Cyberhaven.
A compromised extension with read access can steal patient data. One with write access can alter clinical records or trigger actions that shouldn't happen. That's not just a security problem. It's a patient safety problem. And in healthcare, it's a HIPAA problem. HIPAA doesn't care that the breach happened three layers deep in your vendor stack.
As Ash Roozbehani of Persepolis Law puts it: “What health tech founders often underestimate is that HIPAA is enforced on a “strict liability” basis. If your product causes protected health information to be accessed, disclosed, or exfiltrated in a manner HIPAA does not permit, that is a violation. This is true even if the root cause is a third-party library or a Chrome extension update. Regulators do not need to prove recklessness or negligence; they only need to show that PHI was improperly exposed and that your company was responsible for the system that allowed it.”
The Business Risk
Even if you never get hacked, you're building on a foundation you don't control. Google can change Chrome's extension policies tomorrow. The EHR vendor can implement technical measures to block extensions. One policy update and your product stops working.
And you'll never get official marketplace placement or co-marketing support from the EHR vendor. You're locked out of the ecosystem benefits that come from being a sanctioned partner.
The Better Path
No integration approach is risk-free. But API integrations keep the attack surface on your servers, where you control it, rather than in every user's browser, where you don't. Yes, building to official APIs takes longer. You have to apply for access, work within rate limits, and build to specs instead of scraping whatever you need. It requires more patience upfront. But you get a lot in return. Official support channels. Marketplace visibility. A defensible integration architecture that doesn't depend on Chrome's policies or the EHR vendor looking the other way.
athenahealth's APIs have expanded significantly over the past few years. Many use cases that "required" a browser extension five years ago can now be handled through official endpoints. It's worth checking what's actually available before assuming you need a workaround.
If you're building a real business in health tech, build it on real infrastructure. The shortcut isn't worth it.